Help Isom IGA recover from devasting floods

Crime doesn’t pay, as the saying goes—at least that’s how the saying used to go. In the good old days, criminals had to be physically present to rob you, which meant the risk often outweighed the reward.
But the digital crime of today is a different story. This crime doesn’t involve guns or in-person hold-ups—it involves things we do every day, like opening emails, answering phone calls, or logging on to social media platforms. Worst of all, digital crime is increasingly targeting honest, hardworking independent grocers through ransomware, which means one simple mistake, and your POS system or other important data could be held hostage for a mind-boggling ransom.
What is ransomware?
Ransomware is a form of malware (malicious software) that targets your critical systems and data for the main purpose of extortion, or getting money in exchange for returning your data unharmed. It’s the computer version of holding an employee hostage until you pay up. In some cases, criminals refuse to decrypt files even after you pay the ransom.
According to the FBI, ransomware is the fasting-growing malware threat, with over 4,000 ransomware attacks occurring daily since January 1, 2016. IGA Director of Information Technology Ron Gavrilovic explains the 2019 ransomware landscape is diverse, with security researchers tracking over 1,100 ransomware variants. He says there are many different kinds of malware, including viruses, Trojans, spyware, and ransomware, but ransomware is especially dangerous for businesses. “We’re expecting 2019 to be the most damage done, ever, with ransomware,” Gavrilovic says. We’re talking into the billions.” That breaks down to an average per-store ransomware demand of $224,871 in 2019's first quarter alone, according to retailer reports to Beazley Breach Insights.
How does ransomware affect independent grocers?
Cyber criminals can target anyone, from individuals with a simple home computer or smartphone to large corporations or regional hospitals. Small businesses like independent grocers are particularly vulnerable to an attack because the threat of not being able to do business—especially during the holidays—can cripple the business.
“It’s happening to retailers on a regular basis and it’s really a big concern,” says Associate Wholesale Grocers (AWG) Chief Sales Officer Jeff Patterson, who is working with the AWG team to make sure their retailers are protected. “I think whether it’s small stores, multi-store owners, large regional chains, if there isn’t an immediate heightened awareness to avoid situations like this, there are small retailers that could be put out of business just because it shut them down.”
Criminals know that and will target grocers accordingly. Take, for example, a regional grocer in Northwest Indiana who was hit with ransomware just before Thanksgiving 2018. After an employee unknowingly opened an email that launched a ransomware attack, Strack and Van Til’s POS systems were shut down. Half of its stores closed and there were long lines at the others while they worked to resolve the issue. The police report did not say if this group paid the ransom or resolved the issue on their own, but the stores were reopened in time for Thanksgiving, luckily for them.
In some cases, a store hit by ransomware can also infect their wholesalers. Patterson explains, “They try to find these gaps and start moving through different industries,” finding a hole and unleashing a coordinated attack.
How does ransomware infect my system?
“The most common and effective way ransomware gets into your system is through bogus email, SMS [text] messages, websites that you go to,” Gavrilovic explains. By design, they look to infect the machine or device that you’re on at the time,” he says. From there, it looks to infect other machines that are online and connected to your network.
Ransomware doesn’t care if you access it through personal or professional networks. So an employee might be checking their personal Gmail account on a store computer, click an infected link, and within seconds, your POS could be infected.
What does ransomware look like?
Emails
- An email saying you have a voicemail, with an attached link appearing to be an audio recording of the voicemail. Never click on these links or attachments.
- An email notifying you that your account was hacked and you need to reset your password. This email might look like it’s from the company in question, but never click on a link that asks you to reset your password if you didn’t request it. Instead, delete that email immediately and visit the company’s website by typing in the address on your own. Then you can reset your password directly from your account.
- A request to download an attachment. Sometimes the email will appear as if it’s coming from your company, using buzzwords like “bonus” or “invoice.” Never download an attachment unless it’s from a sender you trust completely and you’re expecting the attachment. Read the email to make sure it introduces the attachment properly and inspect the link—without clicking—to reveal the link destination (learn how to do this in the section below titled, "How can I prevent a ransomware attack?").
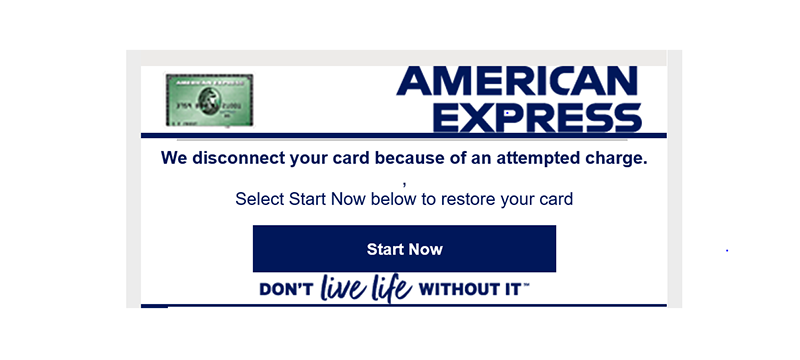
- A notification that the business failed to process your credit card. Usually these emails appear to be from a service you use, like Netflix. Don’t reply or click on these links. Contact the company directly if you are concerned about payment or navigate the website on your own, without using the provided link.
Phone Calls
- Phone calls requesting financial information or passwords. Some callers might claim to be the IRS calling about your tax return, or a representative from the phone or utility company. These companies should never request your full information, like social security number, account number, etc. As IGA CEO John Ross says, “If they ask for complete information, that’s a big warning sign.”
Social Media Credential Updates
- “Social media is very effective for cyber criminals,” says Gavrilovic. He says they create a false sense of urgency by telling you something is wrong with your account and you must login to fix it. Once you click the false link and enter your credentials, the screen will suggest the site is not available, so you close out and go about your day. Meanwhile, the criminals will log in to your account, lock you out of it by changing your password and security questions, and start infecting contacts, friends, or followers. Use extreme caution when receiving password change requests. Always look at the internet address of the website you’re visiting before proceeding to ensure you’re on the page you expect to be on.
Website Copies
- Gavrilovic says many cyber criminals create websites that look so close to the authentic page, mimicking the graphics and design of the page, so that you enter your credentials, which they quickly record and use to access the real websites under your accounts.
Apps
- There are many apps that are created with the sole purpose of infecting your devices and those of your contacts. Many use your location data and information you voluntarily upload to infect your contacts. Only obtain software or apps from known, credible sources.
With so many forms of deception out there, it’s time consuming to remain vigilant. “Everyone is really busy these days, so they don’t want to spend a lot of time analyzing things, which makes these tactics very effective, unfortunately,” says Gavrilovic. “If you’re ever concerned by [potential spam], disengage with these parties, and go on your own—navigate to the website on your own or give them a call.”
How can I prevent a ransomware attack?
“Everyone has to take this really seriously and take a look at what they’re doing,” says Gavrilovic, because it’s very easy for criminals to access your devices or networks, since they don’t have to be physically present to do so and the crime reaps a lucrative return.
Ross advises all IGA retailers to prevent malware and ransomware with these best practices. “If you do these steps,” he says, “you can cut the risk by about 80 percent.”
- Upgrade your machines. Old computers and operating systems are the most vulnerable to an attack. Invest in a newer model and always update your operating system and software applications as new versions and updates become available.
- Purchase antivirus software. Protect your machines and networks with a trusted antivirus software. While it isn’t guaranteed to prevent attacks, it’s another line of defense that should be employed.
- Enable password protection for all publicly accessible machines. Every computer, especially those that can be easily accessed or seen by customers—the computer behind the customer service desk, the registers, etc.—should be password protected so that if an employee leaves the station, no one can gain access to them.
- Create an effective backup strategy. “Backup is your giant safety release valve,” says Ross. Whether you back up your data manually by saving it to an external device regularly and then taking that device offsite, or use an automatic backup service that stores the data in the cloud, if you are hit but you have a disconnected backup, your store will recover more quickly. Contact an IT professional to assess your network and infrastructure to set up the best backup system for your business.
- Train your associates. “It’s very important for your associates to be aware and be trained,” says Gavrilovic. Even if they’re not power users, he says many people are completely unaware of the common risk malware poses. It can happen to anyone, so even a young employee using the store’s Wi-Fi could click an infected link on their phone and infect the store’s network. Training can prevent these easy attacks.
Since so many networks are infected through email, ask yourself these questions and consider these email warning signs.
- Is this someone I regularly do business with?
- Are there a lot of people copied that I don’t know?
- Does the subject line match the content of the email?
- Does the email contain unusually bad grammar, or are there a lot of foreign characters or languages?
- Trust your gut. If it doesn’t feel right, err on the side of caution.
- Does the link seem suspicious? Hover your cursor over the link without clicking—DO NOT CLICK!—and you will see the actual address. If it doesn’t match the email domain or the company it came from, that’s a huge red flag—don’t click.
What happens if my store is hit by a ransomware attack?
Gavrilovic recommends that associates seeing something suspicious send it to the IT professional the store works with or even someone they know with a basic knowledge of IT. He also encourages the store owners and managers to work with their email providers to get suspicious senders and messages blocked and marked as spam. “It helps the entire system that you’re on because it will help identify more examples,” he says.
If you are hit by an attack, Gavrilovic says:
- Immediately disconnect that device from your network.
- Put the infected device to sleep and do not reboot or restart it.
- Contact an IT professional immediately so they can investigate and block access to anything else in your business.
He says it only takes an average of three seconds to start infecting a system once an attack is triggered, so taking these immediate steps is crucial to slowing the virus to minimize how much it can infect.
How can I learn more?
IGA is working to get retailers more information and best practices to prevent a ransomware attack. As Ross says, “We’re a service organization, and we can’t visit every store and do a security audit, but it is our obligation to ensure our retailers win.”
These tips are the beginning of more training that will be available soon, so stay tuned to The IGA Minute for more information coming your way in 2020--including two new courses from the IGA Coca-Cola Institute. In the meantime, please review the FBI’s detailed recommendations for ransomware prevention and response here.
If you follow the best practices outlined above, pair them with Gavrilovic’s key takeaway. “Always remember to slow down,” he says. “This false sense of urgency always creates a lot of this, so please take a step back and make sure it makes sense to you before you click.”
Watch the below webinar from IGA CEO John Ross and Director of Information Technology Ron Gavrilovic for more information and tips on preventing and fighting ransomware attacks.
Next Story
Fix the Retail Glitch →
No Comments Yet
Let us know what you think